April is the cruelest month
This April has been a wild ride. At the start of the month, Anthropic made bold claims about the security research abilities of its Claude Mythos model. Any open source project under the sun is now in the danger zone, and Dangerzone even more so.
In the past few days, we became aware of some AI-assisted vulnerabilities that could affect Dangerzone, but thankfully are mitigated by our defenses.
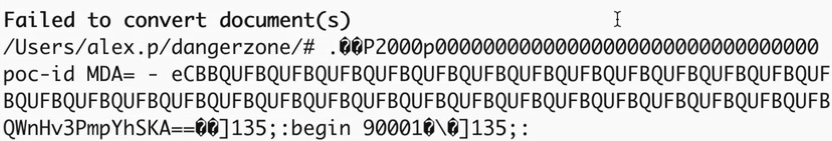
On April 17, a security team disclosed that iTerm2 was vulnerable to a PTY confusion attack. The details of the attack and its impact are not what matter here, but the crucial point is that there are popular terminal emulators out there that may parse untrusted output and perform actions based on it. Our dangerzone-cli, the CLI counterpart to the Dangerzone GUI, does handle untrusted content and may print it to the terminal, but thankfully, it sanitizes it first:
We were aware of this attack vector from internal research we had performed a while back, which was the result of our first-ever security advisory.
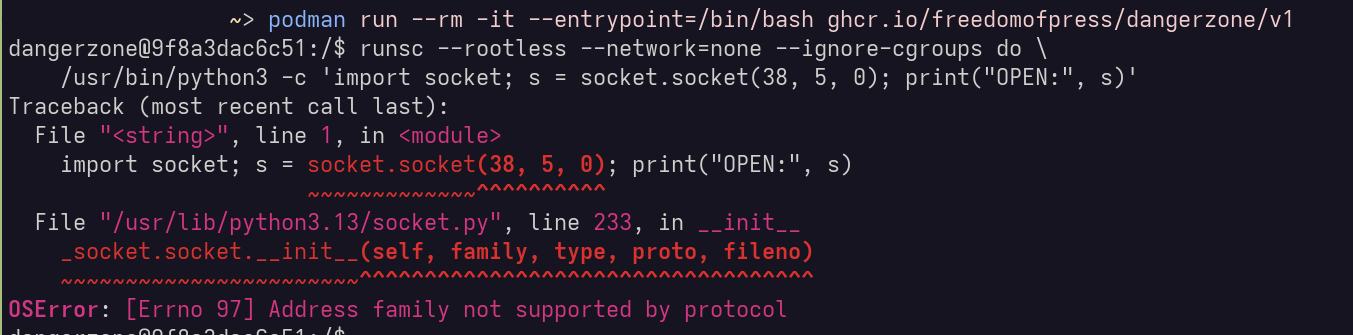
On April 29, the copy.fail vulnerability was disclosed by another security team. This vulnerability allows any unprivileged user in the system to gain root privileges on any Linux system since 2017, via an exploit in the kernel crypto API (AF_ALG). This would theoretically affect all of our users, since Dangerzone uses Linux VMs to run its sandbox, even on Windows and macOS.
Our gVisor integration, though, saved the day:
We are confident that our security measures in place will still hold for the foreseeable future, but ne'er cast a clout till May be out!